What Your Networked AV Projects Must Change Under Germany’s NIS2 Law
Germany’s NIS2 law is now in force. If you deliver networked AV in Germany, this is not background noise but a design constraint.
The EU’s NIS2 Directive - Directive (EU) 2022/2555 on measures for a high common level of cybersecurity across the Union -- required national transposition by October 2024. Germany missed that deadline and faced formal action from the European Commission, which formally notified Member States for failing to transpose on time in November 2024, including Germany (see the Commission’s update on the NIS2 Directive transposition status). Berlin then moved. The act was passed in November 2025 and entered into force in early December 2025, a timeline reflected in multiple legal briefings, including Freshfields’ analysis of Germany’s NIS2 implementation entering into force on 6 December 2025.
You can find the law itself here: NIS2 Implementation and Cybersecurity Strengthening Act, and the European Commission’s narrative on German implementation, here. Seek it out by all means, but for Pro AV professionals, the legal detail is somewhat secondary. The commercial impact is not.
More German organisations now fall under stricter cybersecurity obligations. Senior management carries clearer accountability. Incident reporting duties tighten. Supplier oversight becomes formal rather than informal. This all flows straight into tenders, technical submissions, and contract language.
If your AV system touches the client’s network, you are part of that conversation.
Why Germany’s NIS2 law matters to networked AV
Germany’s NIS2 law changes the tone of procurement. It widens the scope of organisations under cyber obligations and forces tighter supplier scrutiny, including AV.
If you want the short version before we go deeper, here it is.
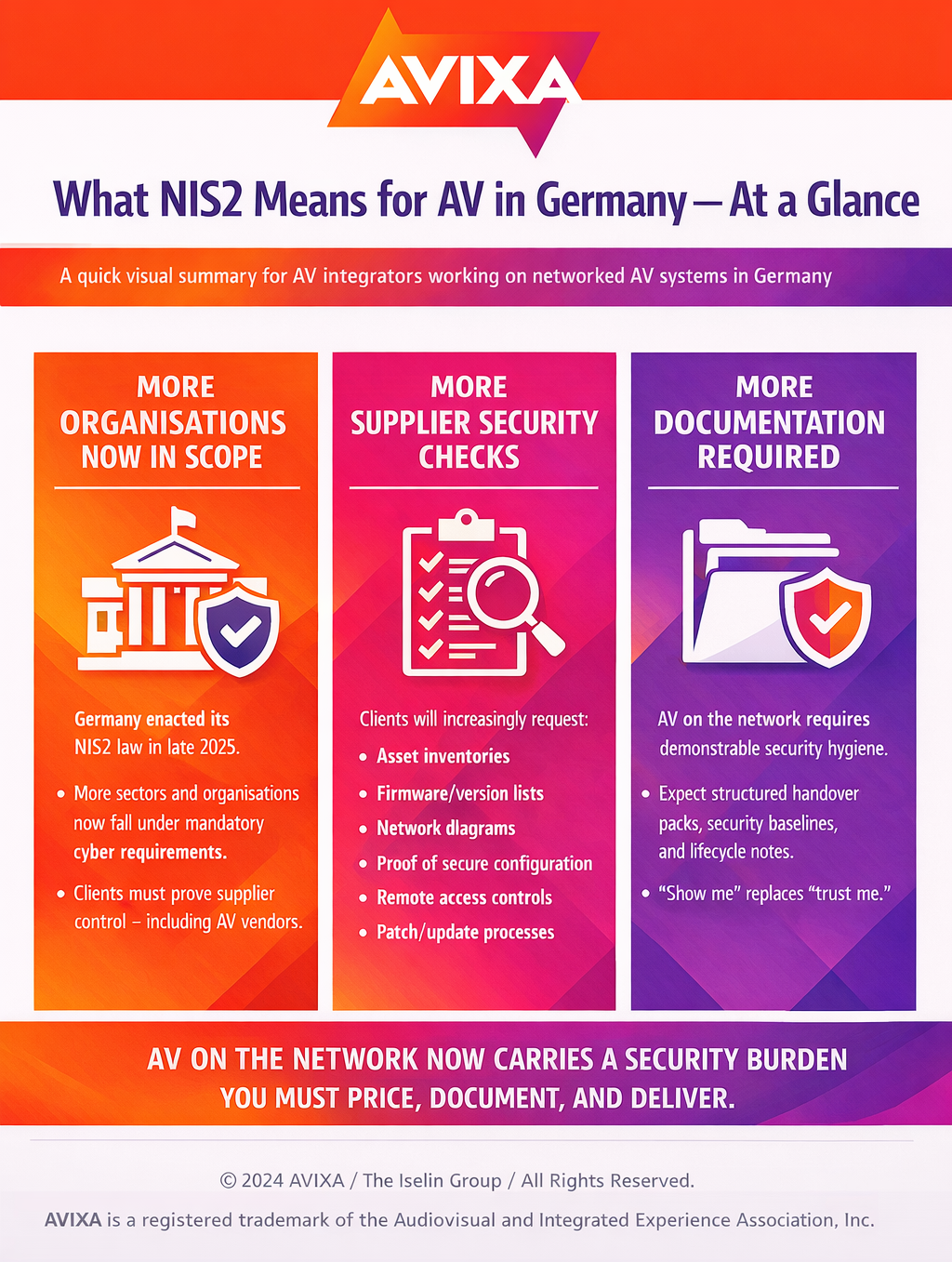
Figure 1: What NIS2 means for AV in Germany — at a glance
That’s the high-level shift.
Now let’s break down what this means for your next tender, your next IT review, and your next handover pack.
Networked AV cybersecurity used to sit in a grey zone. IT worried about it. AV teams worked around it. Procurement teams rarely dug deep unless the client was already heavily regulated.
Germany’s NIS2 law changes the tone. It does not suddenly make AV integrators “regulated entities” in most cases. It does mean your clients must show that they manage supplier risk. This includes your organization.
Modern AV systems are not isolated racks. They are AV-over-IP endpoints, unified communications (UCC) room systems, digital signage players, control processors, cloud dashboards, and remote monitoring tools. They sit on enterprise networks. They carry sensitive audio and video. They often expose web interfaces. They rely on firmware updates and remote access.
Under NIS2 pressure, German IT teams treat those elements as part of their cyber risk register.
AVIXA’s Recommended Practices for Security in Networked Audiovisual Systems already frames security as a shared responsibility across end user, integrator, consultant, and manufacturer. Germany’s new legal environment gives that guidance sharper teeth. What was good practice becomes procurement expectation.
If you bid in Germany, assume that networked AV cybersecurity will be examined early, not as an afterthought.
What changes in tenders under Germany’s NIS2 law
The first impact is the paperwork. The second is the process.
Expect more supplier questionnaires that look like they were written for IT platforms rather than AV systems. Expect security sections in RFPs to expand. Expect legal teams to insert clauses on incident notification, vulnerability handling, and patch management.
German buyers will ask for evidence, not promises.
They will want:
- A full asset inventory: device model, firmware version, location. – A network diagram showing segmentation and management access.
- A description of remote access mechanisms and how they are controlled.
- A patching and update process, including post-handover ownership.
- A clear allocation of responsibilities between AV integrator, IT department, and manufacturer.
None of this is exotic. What is new is the insistence.
AVIXA’s Pro AV Trends article on securing AV systems against network threats sets out the basics: segmentation, controlled access, firmware discipline, and documented processes. Under Germany’s NIS2 law, those basics become audit artefacts with the AV tender path including a formal cyber checkpoint.
Cybersecurity in AV is no longer just a technical discussion. It’s a procurement and accountability issue. AVIXA’s panel on regulation and responsibility captures that shift clearly:

And here’s what that flow, treated as a new AV tender path under NIS2, looks like in practice.
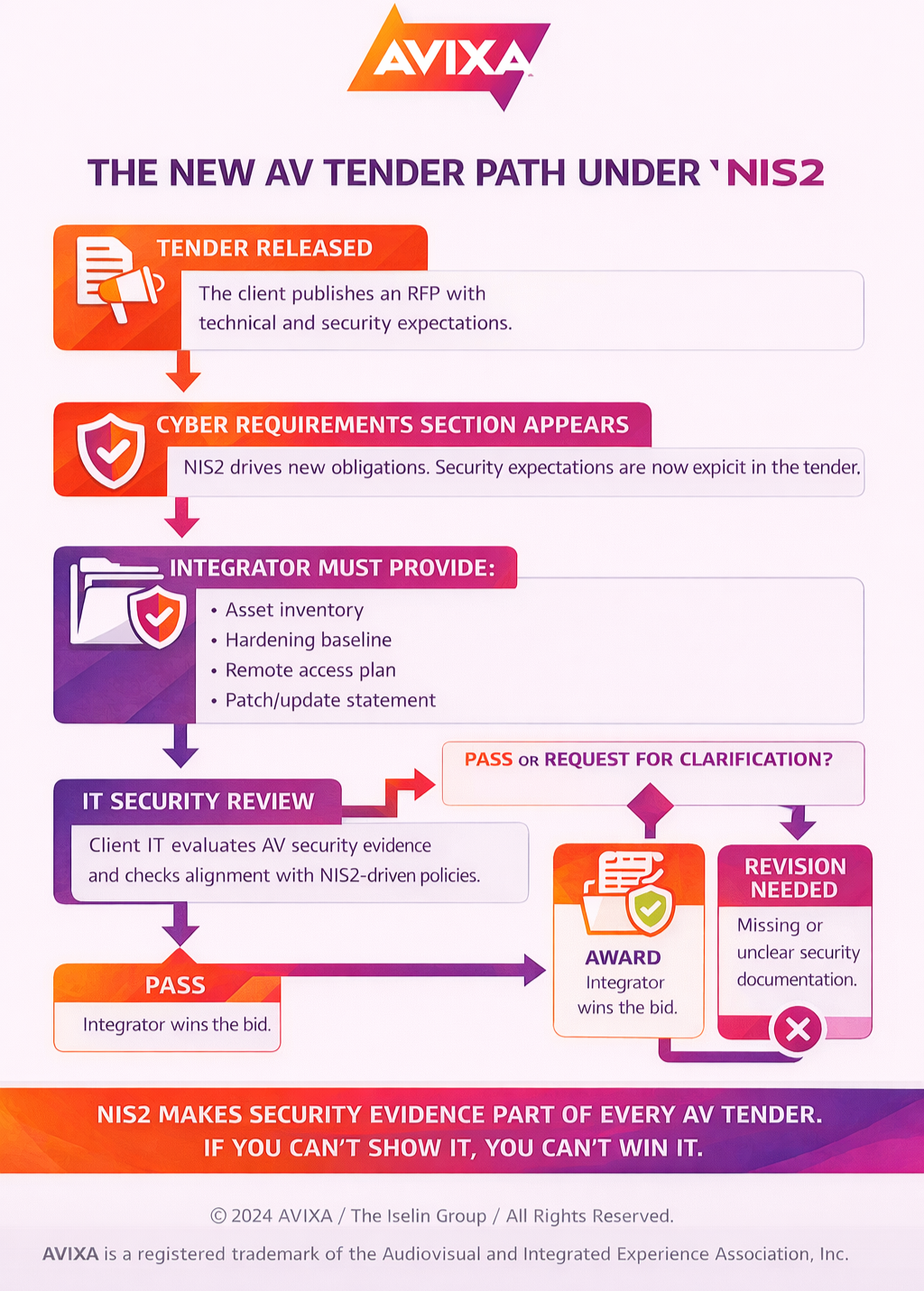
Figure 2: NIS2 turns AV security evidence into a bid gate. No documentation, no award
If your documentation is clean, you move forward.
If it’s vague, incomplete, or improvised, you loop back — or you lose the bid.
That’s why delivery discipline now matters as much as system performance.
Where networked AV projects break
You know the scene.
You are days from go-live. The AV-over-IP network is stable. The room sounds clean. The control interface is signed off. Then IT asks for the security documentation pack.
They want to know which ports are open on each endpoint. They want confirmation that default credentials are gone. They want to know how remote access is granted and revoked. They want to know whether firmware updates are tracked. They want clarity on who owns patching after handover.
If you do not have answers in writing, the schedule slips. The tension rises. The cost shifts onto you.
Germany’s NIS2 law increases the likelihood of that moment. It also increases the cost of getting it wrong. Organisations under NIS2 pressure cannot afford to wave through undocumented systems.
For networked AV projects, that means security must be built into delivery, not layered on at the end.
The delivery changes you should make now
Start with design.
Security decisions made during commissioning are expensive and messy. Design segmentation, management access, and update workflows before hardware is ordered. This avoids late reconfiguration and political fights between AV and IT.
Adopt a standard hardening baseline for every networked AV build. Change default credentials. Disable unused services. Use secure management protocols. Restrict web interfaces. Keep firmware current. Record the shipped version numbers.
Make this baseline part of your internal quality control, not a special request from the client.
For practical AV language that maps well to IT expectations, AVIXA Xchange’s piece on AV networking security best practices provides a clear, no-nonsense checklist.
Next, address segmentation properly. AV-over-IP performance depends on bandwidth and multicast control, but that does not require a flat network architecture. Separate media traffic from management traffic. Limit administrative access to defined subnets. Use access control lists on switches. Provide the client with a clean network diagram as part of the handover.
Segmentation is not only about security. It reduces the blast radius when something fails. It makes troubleshooting faster. It demonstrates control.
Next, clean up remote access.
If you rely on VPN access, define how it works. If you use vendor cloud portals, define how they are controlled. Document who can access systems, how access is approved, and how access can be revoked. Avoid shared administrator passwords wherever the platform supports named accounts. Where it does not, document compensating controls.
Remote access is not a convenience feature. Under Germany’s NIS2 law, it is a governance issue.
Finally, transform handover into an operational document set. Include the asset register, firmware list, network map, access control description, patching plan, backup procedures, and responsibility matrix. German IT teams need artefacts for audit and reporting. If you supply them cleanly, you reduce friction.
Contract language and supplier risk
Germany’s NIS2 law sharpens contract language.
Watch for vague clauses requiring you to “ensure compliance” with broad cybersecurity duties. Clarify scope. Define what you control and what the client controls. Specify who manages updates, who monitors logs, and who handles incident reporting.
A simple RACI model/responsibility matrix — who is Responsible, Accountable, Consulted, and Informed — prevents later conflict.
For example:
- AV integrator responsible for secure configuration at handover.
- Client IT accountable for ongoing patch management after sign-off.
- Manufacturer consulted for vulnerability advisories.
- Both informed of incidents affecting shared infrastructure.
Write this down before the project starts. It protects margin and reputation.
Monitoring and logging: the next wave of questions
German IT teams under NIS2 pressure are improving their monitoring maturity. They will ask whether AV systems produce usable logs. They will ask whether configuration changes are auditable. They may ask whether alerts can integrate with existing monitoring tools.
Be clear about what your chosen platforms support. If logging is limited, say so. Mitigate with segmentation and controlled access. If advanced logging is available, price and enable it.
Operational resilience matters here. Many AV failures are operational, not malicious. Under stricter governance, resilience and cybersecurity sit closer together. This supports a stronger business case for managed services and lifecycle planning.
If you frame monitoring as risk reduction rather than feature creep, German buyers will listen.
Manufacturer choice under Germany’s NIS2 law
Supplier scrutiny extends to your vendors.
Clients will ask whether manufacturers publish security advisories, provide regular firmware updates, and state clear end-of-support timelines. They will ask whether devices support secure management protocols and whether unnecessary services can be disabled.
If you cannot answer these questions for your chosen product lines, you will struggle in regulated sectors.
This does not mean only large vendors survive. It means integrators must understand the security posture of the products they specify.
Cheap hardware with weak update discipline becomes expensive when it triggers IT concerns. Germany’s NIS2 law shifts the cost calculus.
Pricing the work properly
Security work costs time. Design coordination with IT costs time. Hardening costs time. Documentation costs time. Managed update services cost time.
If you do not price that effort, you will perform it anyway under pressure.
Make networked AV cybersecurity a visible line item. Tie it to regulatory expectations and risk control. Explain the deliverables: segmentation plan, hardening checklist, asset register, remote access policy, and handover pack.
German buyers respect clarity. They do not respect vague reassurance.
Under Germany’s NIS2 law, security is not optional polish. It is a deliverable.
Security under NIS2 is no longer a configuration detail. It’s a documentation discipline. If you deliver a system without structured security evidence, you’re handing the client’s IT team a risk problem — and yourself a bid problem on the next job.
A proper handover now needs to look like an operations pack, not a verbal assurance. That means defined ownership, documented baselines, lifecycle notes, and evidence that someone is accountable after you leave the site.
Make handover an ops pack and show you really know your way around cybersecurity.
If your current handover doesn’t contain most of what’s above, expect friction. German IT departments are now under formal security obligations. They will ask for documentation. They will escalate unclear ownership. They will delay sign-off.
The difference between winning and looping in clarification often comes down to whether you can produce this structure up-front and without scrambling.
Price it. Scope it. Build it into your project timeline. Once security documentation becomes part of the tender gate, improvisation stops working.
My Verdict
If you deliver networked AV in Germany, treat the German NIS2 law as a delivery standard, not background compliance noise.
Build a repeatable security baseline into every AV-over-IP and UCC project. Document it. Hand it over properly. Clarify responsibilities in writing. Price the effort honestly.
Do this, and you reduce last-minute IT blocks, win tighter tenders, and protect your margin. Ignore it, and your systems will be tagged as risk, then replaced.
Germany has made its move. Now you need to make yours.
References for Figure 2: The New AV Tender Path Under NIS2
NIS2 baseline obligations that create the "security evidence" expectation
EUR-Lex — Directive (EU) 2022/2555 (NIS2 Directive), Official Journal
EU-level summary and implementation framing
European Commission — NIS2 policy page
Germany's official authority landing page for NIS2-regulated organisations
BSI (Federal Office for Information Security) — "NIS-2 regulierte Unternehmen"
AVIXA security recommended practice
AVIXA Standards — Recommended Practices for Security in Networked Audiovisual Systems
AVIXA editorial guidance on practical security steps
AVIXA Pro AV Trends — Securing AV Systems Against Network Threats