Post-Quantum Cryptography and AV Systems: Why Your Installed Base Has a Crypto Expiry Date
A typical AV deployment runs for a decade. With that in mind, think about the systems currently being specified for conference rooms, signage networks, or control environments. They will still be operating well into the 2030s. That hardware lifespan is normal for Pro AV.
Consider a large enterprise estate: 600 meeting rooms deployed across Europe between 2024 and 2027. Every room contains networked AV endpoints that verify firmware updates and remote management access using today’s public-key cryptography. If those devices cannot change algorithms later, the trust chain expires the moment post-quantum standards become mandatory. The displays will still work. The microphones will still capture audio. What fails is the mechanism that proves software is legitimate. The hardware can stay functional while the fleet becomes impossible to defend.
The security assumptions inside those systems may not last nearly as long.
Post-quantum cryptography has moved from theoretical research into practical engineering discussions. Quantum computing threatens the public-key encryption methods used across the internet and in most connected AV platforms. If those methods weaken within the working life of installed systems, equipment considered secure at commissioning becomes decryptable later.
That is the real risk the AV industry must address.
At ISE 2026, cybersecurity specialist Shaun Reardon from DNV Cyber delivered a blunt warning during the session Unlocking Tomorrow: Quantum Threats and the Future of Security. His message was straightforward: cybersecurity has become a business risk, and the timeline for quantum-capable decryption is short enough (roughly five years) to affect technology deployed today. The session formed part of the ISE 2026 Cybersecurity Megatrend programme.
In this AVIXA TV interview recorded at ISE 2026, Reardon explains why post-quantum cryptography is becoming an operational concern for AV deployments today.
Reardon argues that the real exposure lies in the long lifecycle of AV systems. Networked displays, conferencing endpoints, and control systems often remain in service for a decade or more—long enough that today’s encryption assumptions may no longer hold. If those platforms cannot update their cryptographic foundations, organisations could find themselves operating fleets of otherwise functional devices that no longer meet modern security expectations.
Networked AV Now Depends on Encryption
Ten or fifteen years ago, most AV systems operated on isolated networks.
Serial connections dominated. Control processors and signal paths remained separated from enterprise IT infrastructure. Security planning usually stopped at password protection.
Those conditions no longer exist.
Modern AV installations connect directly to corporate networks and cloud platforms. Meeting room devices authenticate to management services. Digital signage players verify software updates through signed packages. Control systems rely on secure transport protocols when communicating with remote monitoring platforms.
Each of those processes relies on cryptographic trust.
Public-key encryption forms the foundation of that trust. It allows systems that have never met to establish secure communication. Certificates, authentication tokens, encrypted tunnels and firmware signatures all depend on it.
Reardon pointed out how easily this dependency goes unnoticed. AV equipment still looks like a passive endpoint. A display shows content. A speaker outputs audio.
Once those devices operate over IP networks, they become fully fledged computing nodes with the same security exposure as other connected systems.
Why Quantum Computing Changes the Equation
Quantum computing does not replace traditional computing.
Instead, it introduces a different way to solve certain mathematical problems.
Conventional computers process binary states—ones and zeros. Quantum systems use qubits that represent multiple states simultaneously. That property allows them to evaluate large numbers of possibilities in parallel.
Several widely used encryption algorithms rely on mathematical problems that classical computers cannot realistically solve. Those problems become easier for quantum algorithms.
Public-key cryptography is particularly vulnerable.
The internet relies heavily on algorithms such as RSA and elliptic-curve cryptography. Breaking them through brute force would take classical computers an impractically long time.
Quantum algorithms shorten that timeline dramatically.
Researchers have studied this challenge for years. The United States National Institute of Standards and Technology has run a long evaluation programme to identify encryption schemes resistant to quantum attacks. The project and candidate standards can be explored through the NIST Post-Quantum Cryptography initiative.
Several algorithms are now progressing toward standardisation.
This is no longer theoretical planning. The U.S. National Institute of Standards and Technology (NIST) is finalising post-quantum cryptography algorithms, and national cyber agencies are urging organisations to inventory systems that rely on current public-key infrastructure. Boards are starting to ask a simple question: which technologies installed today will still be cryptographically trustworthy in ten or fifteen years? For AV environments with decade-long lifecycles, that answer increasingly depends on whether devices can adopt new algorithms without replacing the hardware.
These developments will eventually filter through operating systems, networking hardware, and cloud infrastructure. The same cryptographic libraries will appear inside AV platforms.
The problem is the transition period.
The Installed Base Problem
AV systems stay installed for years. Video walls in operations centres often run for fifteen years or longer. Digital signage estates may use the same playback hardware for a decade. Meeting room infrastructure is replaced only when organisations change collaboration platforms or undertake major building upgrades.
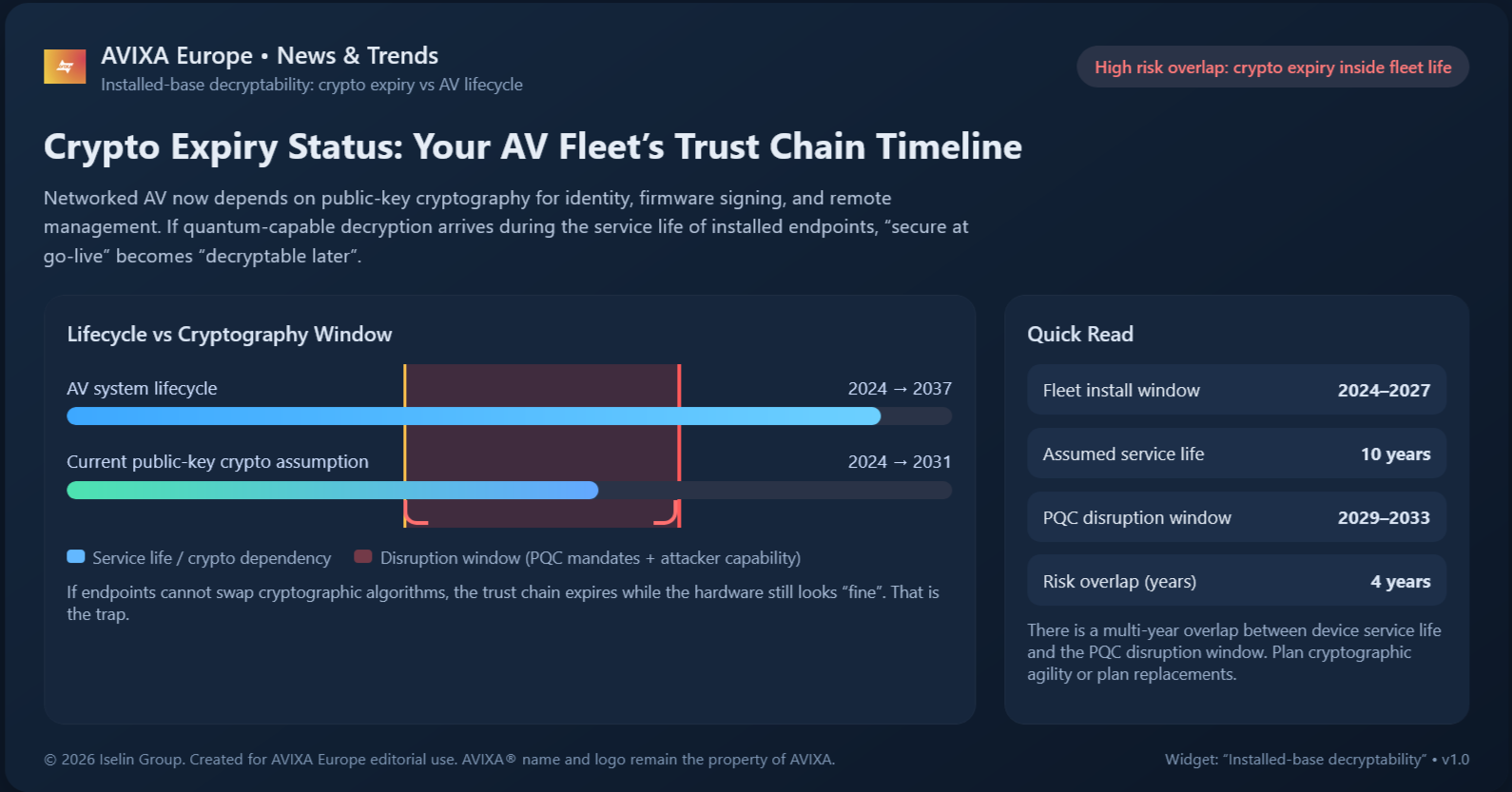
Disclaimer: Timeline values are illustrative estimates based on typical AV system lifecycles and widely discussed quantum‑security projections (e.g., UK NCSC and NIST analyses). Dates shown are not regulatory deadlines or formal predictions. Actual post‑quantum transition timing may vary, and organisations should evaluate crypto‑agility based on their own platforms and risk profiles.
This chart illustrates the installed-base cryptography trap facing networked AV systems. Professional AV deployments often remain in service for a decade or more, yet the public-key cryptography that secures device identity, firmware signing, and remote management may become obsolete much sooner as post-quantum standards emerge. The shaded red band highlights the critical overlap period: hardware that still functions perfectly may no longer meet security requirements because the underlying trust chain has expired.
Unless devices support cryptographic agility—the ability to adopt new algorithms without replacing hardware—organisations risk running fleets that work operationally but fail security audits or vendor support expectations. Normal lifecycles collide with the expected timeline for quantum cryptography disruption.
If quantum-capable decryption becomes practical within the next decade, systems installed today will still be active when that happens. The encryption protecting them may weaken before the hardware reaches end of life.
That does not mean every AV device will suddenly become insecure overnight.
It does mean trust relationships embedded in those systems may degrade.
Certificates identifying devices, cryptographic signatures verifying firmware, and authentication mechanisms protecting remote management all rely on long-term encryption assumptions. When those assumptions weaken, attackers gain new opportunities.
“Harvest Now, Decrypt Later”
The problem becomes even clearer in large device fleets. It reflects what cybersecurity teams describe as the “Harvest Now, Decrypt Later” (HNDL) problem, which Reardon articulated plainly: attackers can “harvest now, decrypt tomorrow.”
The strategy is simple. Attackers collect encrypted communications today and store them. When stronger computing capabilities become available, they decrypt the archived data. This approach already appears in long-term cyber-espionage operations.
For AV infrastructure, the implications depend on system longevity. Meeting room platforms exchange encrypted authentication traffic every day. Signage networks communicate continuously with content servers. AV-over-IP deployments transmit control and monitoring data across secure channels.
If those communications are intercepted and stored, they remain potentially readable later.
Encryption protects more than confidentiality.
Firmware signing is another critical control. Many AV devices verify software updates using cryptographic signatures to prevent tampering. If attackers eventually forge those signatures, malicious updates could appear legitimate.
That scenario turns a security safeguard into a potential attack path.
AV’s Role Inside Operational Networks
The consequences extend beyond data protection. AV systems increasingly operate alongside operational technology (OT). OT refers to digital systems controlling physical equipment—manufacturing lines, energy infrastructure, transport networks, and other industrial environments.
Video walls, monitoring displays and control interfaces form the human interaction layer for those environments.
Reardon’s work includes cybersecurity assessments across offshore platforms and industrial facilities. In those environments, the boundary between IT systems and operational networks is already sensitive.
Compromising an office computer might lead to financial loss.
Compromising infrastructure controlling machinery introduces safety risks.
AV equipment does not usually operate machinery directly. However, it provides visibility into those systems and often shares network infrastructure with them. That position makes AV endpoints potential entry points for attackers targeting operational environments.
As AV integration with enterprise and operational networks grows, its security assumptions matter more.
Post-Quantum Cryptography Is Emerging Now
The security community recognised the quantum threat long before practical machines appeared.
Post-quantum cryptography refers to encryption techniques designed to resist both classical and quantum attacks.
Researchers have spent years evaluating candidate algorithms. NIST has now selected several schemes for standardisation following extensive analysis.
Two of the most prominent are CRYSTALS-Kyber for key exchange and CRYSTALS-Dilithium for digital signatures.
Technology vendors are already testing hybrid encryption models that combine traditional algorithms with post-quantum alternatives. This approach allows gradual migration while maintaining compatibility with existing systems.
Networking platforms, operating systems and cloud services will introduce these mechanisms first.
AV platforms typically adopt security frameworks provided by those environments.
It is also important to understand where the risk actually sits in an AV system. The HDMI signal between a laptop and a display is unlikely to be the weak point. The exposure sits higher in the stack: device identity certificates, firmware-signing systems, remote-management authentication and any data that must remain confidential for many years. In other words, the vulnerability lies in the trust infrastructure that allows large fleets of AV devices to operate safely on enterprise networks—not in the video signal itself.
What AV Engineers Should Examine
Quantum computing itself is not the immediate operational issue. Adaptability is.
Systems must be able to replace encryption methods during their working life. Security specialists describe this capability as crypto agility.
Crypto-agile systems allow encryption algorithms to change through software updates rather than requiring hardware replacement. Devices without that flexibility may become difficult to secure once encryption standards evolve.
This distinction will influence long-term reliability of AV infrastructure.
Engineers managing large deployments should pay attention to how vendors handle certificates, firmware signing, and update mechanisms. Products that support structured update processes can adapt more easily to new cryptographic requirements.
Systems designed without that flexibility risk becoming stranded.
The industry has already faced similar transitions. Early versions of the Secure Sockets Layer (SSL) protocol once protected most internet communications. As vulnerabilities appeared, SSL was replaced with modern Transport Layer Security (TLS) standards. Devices unable to upgrade their encryption became obsolete.
The same pattern will repeat with quantum-resistant cryptography.
My Verdict
Quantum computing will not suddenly break every AV system. The bigger issue is quieter: many installed systems will outlive the encryption assumptions that protect them. That reality turns cryptography into a lifecycle engineering concern.
Manufacturers must design products that can update their security foundations through software. Integrators need visibility into how platforms manage certificates, authentication and firmware trust. Enterprise AV teams should treat encryption support as part of platform longevity.
Ignoring the issue does not produce immediate failures. It produces systems that remain operational while gradually losing their ability to prove they are trustworthy. For an industry built around long-life infrastructure, that is the security challenge that matters.
Image source: Getty Images / Vertigo3d




.png?sfvrsn=526c0e8b_1)